“Transifex makes it effortless for our dispersed team of web engineers, SEO, campaign managers and content marketers to manage the entire localization process.”

Lift language barriers and
engage the world
Grow revenue and take your business global
with AI empowered translation and localization.

human-quality
translations at scale
empowered by AI
Translations that sound authentic and on-brand,
at record speeds and minimum costs. Transifex AI provides
context-based translations at scale while making it extremely
easy to fully adapt content to your needs.
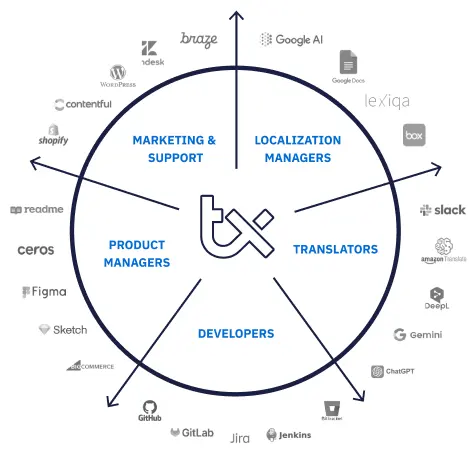
the one localization hub
for your entire process
Bring all your content from multiple sources into one platform
and be fully in control of your localization process. Collaborate
with your team effectively and simplify your workflow. Never
worry about lost email and outdated Excel sheets again.
built to manage even
the most advanced
workflows
Eliminate manual tasks from your day-to-day activities. Automate
workflows, manage all tasks in one place, automatically translate
content based on your trained algorithm, and publish your work
faster than ever.